
Vanessa Gilmartin, AIG’s Global Operations Claims Process Lead, applies the same dedication and foresight to ensuring outstanding claims service and competing in triathlons

Vanessa Gilmartin, AIG’s Global Operations Claims Process Lead, applies the same dedication and foresight to ensuring outstanding claims service and competing in triathlons

Over 160 AIG Analysts and Apprentices gathered at the AIG North America Early Careers Summit outside New York City for a week of sessions to hone their professional and insurance skills.

Glatfelter President and CEO Erin Fry is leveraging product innovations, distribution partnerships and a culture of caring to help clients quickly recover in moments that matter.

Karen Jury, Head of Multinational, AIG UK, shares how her team helps clients navigate local insurance regulatory environments to expand with confidence and capture tomorrow’s opportunities.

U.S. Marine Corps Veteran Chris Bumgardner shares how the learn-it-all mindset he developed in the military informs his leadership at AIG to offer best-in-class global claims service.

The recognition underscores AIG and The R&A’s continued efforts to elevate the quality of the Championship to new heights.

The AIG Women's Open champions women's golf with historic prizes and initiatives that push the sport forward.

This incredible milestone represents AIG’s first upgrade from Moody’s since 1990 and the first upgrade from S&P since 2013.

AIG’s 2025 summer interns reflect on the hands-on experience, valuable professional networks and vital industry skills they gained from their time at AIG.

AIG is proud to join the Salford City Football Club (SCFC), an English professional soccer team, as a minority equity investor and long-term commercial partner.

As the proud title sponsor of the AIG Women’s Open, our colleagues around the world share how the skills they use while golfing translate directly to how they deliver excellence for AIG’s clients.

AIG is the proud title sponsor of the 2025 AIG Women’s Open, bringing together the world’s most celebrated golfers to compete for the top prize in Wales, July 31 – August 3.

AIG welcomed a group of Howard University business students to the New York headquarters to learn more about AIG's Purpose and Values, inclusive workplace and opportunities for growth.

Borregaard, one of the world’s most advanced and sustainable biorefineries, expands its existing cover with AIG.

AIG leaders gathered near the new innovation hub in Atlanta, Georgia, to underscore its important role in advancing our data and digital strategy

Participants in and alumni of AIG’s Early Career reflect on why volunteering is important to them.

For the third year in a row, AIG has earned the 2025 Handshake Early Talent Award, which recognizes AIG as one of the best places for Gen Z professionals to grow their careers.
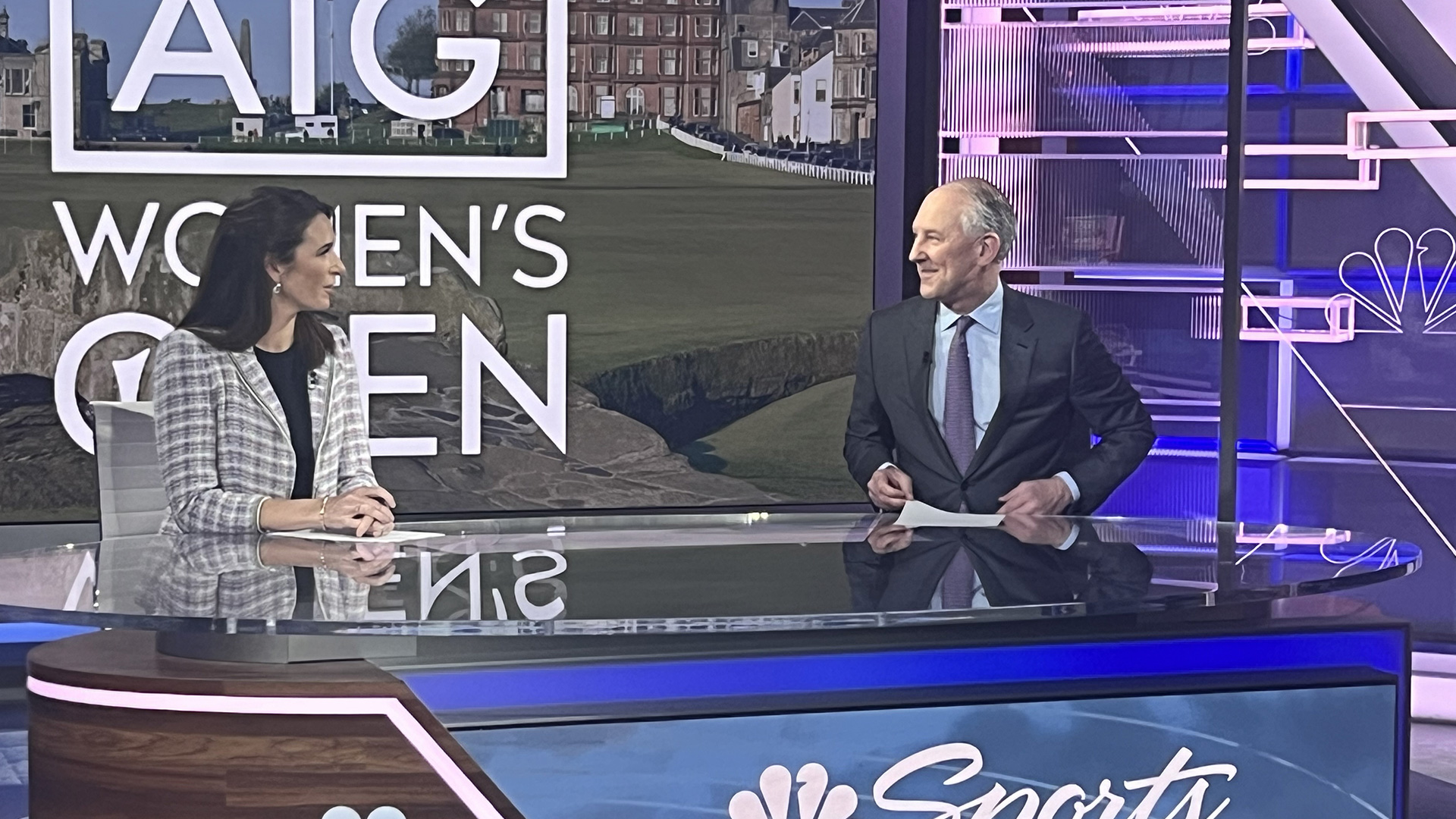
AIG Chairman & CEO Peter Zaffino recently spoke with NBC Sports and Golf Channel host, Cara Banks, about the 2024 AIG Women's Open at St Andrews, and our motivations for being the title sponsor of the Championship since 2019.

AIG and The R&A have worked together to provide an exceptional player experience.

AIG Chairman & CEO Peter Zaffino and AIG Global Ambassador Georgia Hall share actions they have taken to prepare to lead and inspire the next generation of talent from their respective fields.

Dennis Froneberg, AIG’s Managing Director for the DACH region, discusses how auto manufacturers and their suppliers can manage potential risks as they invest more in electric vehicles.

The Belgium-based circular materials technology company needed more than a traditional insurance policy.

Dominik Bark, AIG’s Head of Financial Lines covering EMEA, shares how AIG helps clients position their organizations for long-term growth across the region.

Don Bailey, AIG’s Global Head of Distribution and Field Operations, is deepening the insurance organization’s partnership with brokers to help clients succeed in today’s complex marketplace.

Through golf clinics and academies, the insurance organization encourages women in business to learn the game, network and have fun.

The AIG Ambassador discusses key qualities she sees in her allies.

Jill Dixon, AIG Multinational’s Chief Operating Officer, is utilizing data and technologies to help brokers and clients manage risks they may be overlooking.

Inside AIG Programs and how decades long relationships help assure the future at AIG.

AIG Global Chief Claims Officer Anthony Vidovich is helping clients and brokers get what they need when it matters most.

Claude Wade, AIG Executive Vice President, Chief Digital Officer, and Global Head of Operations, is leading strategies to reimagine brokers’ and clients’ digital experiences.

As Head of Financial Lines in Sub-Saharan Africa, Roxanne Griffiths supports clients with tailored insurance solutions.

As head of the Accident and Health business covering the Europe, the Middle East, and Africa region, Martin Jorgensen is supporting the health and well-being of the communities AIG serves.

Attracting, developing, and retaining top talent is key.